Blue Team Labs Online - Sandbox

Reverse Engineering
Tags: LiSa Sandbox Virus Total Command Line URLHaus
Scenario For the past few weeks, you’ve been analysing files continuously and it’s starting to take its toll on you. After some thought, you realised that automating some of your analysis work could not only save time but avoid mistakes that can arise from the constant focusing while analysing. Analyse the samples provided on the sandbox provided.
Sandbox location: localhost:4242
Investigation Submission
Q1) What is the username for the creator of the sandbox on GitHub? (Format: Username)
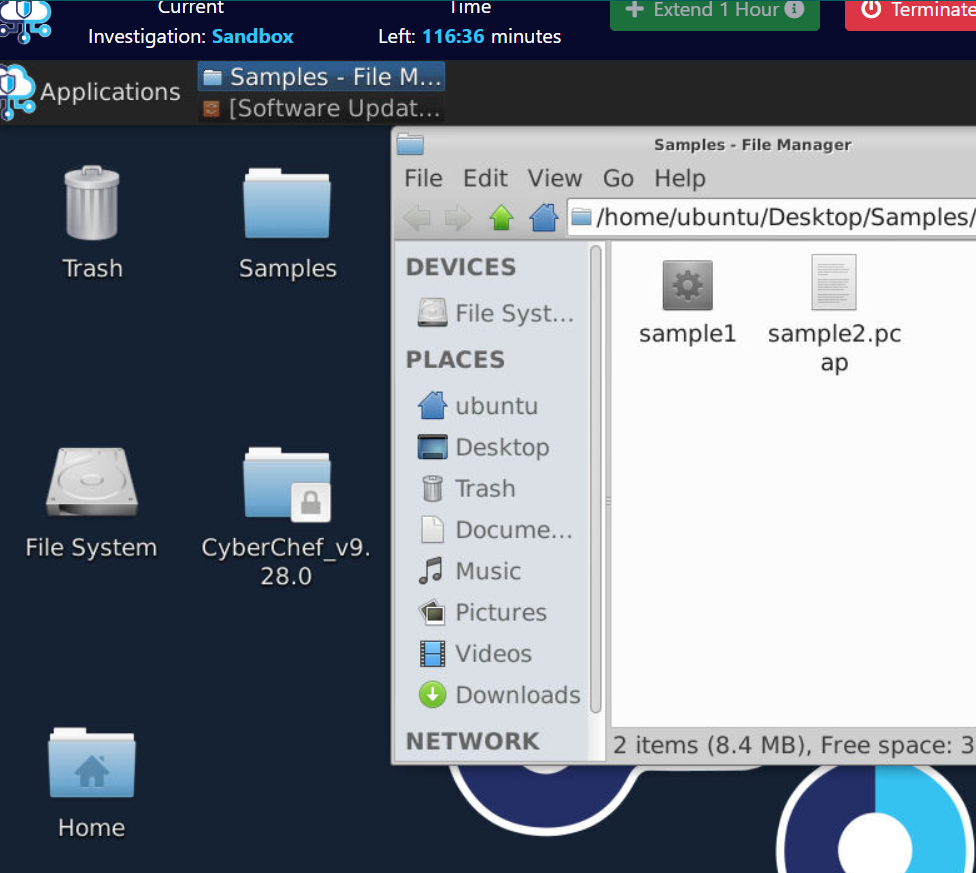
We got 2 samples inside Samples directory on the desktop but we have to use them on Q2 so lets osint for this Q
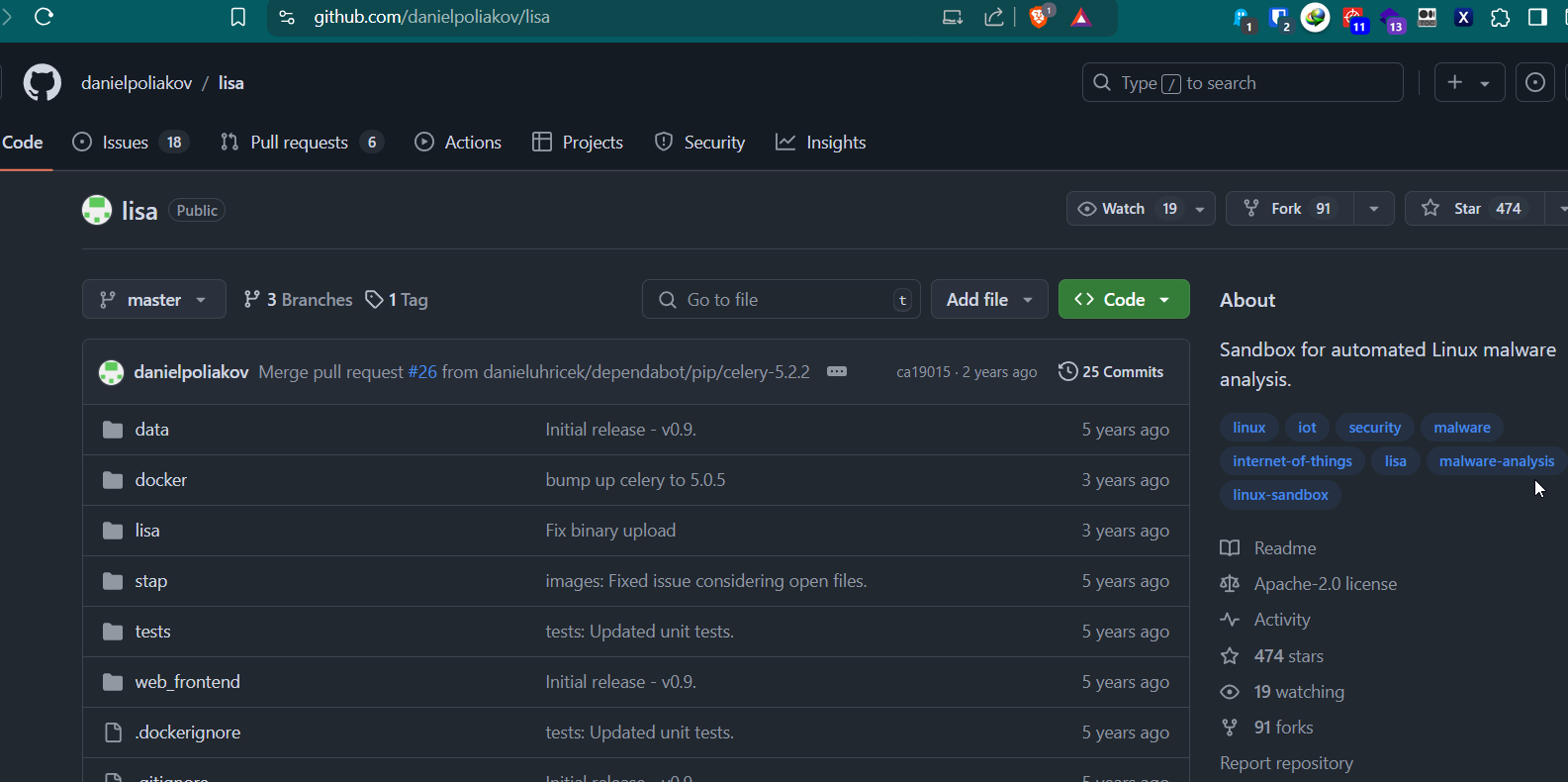
If we searched for lisa sandbox then we will eventually find this github repo but we could not submit this username as the answer, maybe the username was changed?
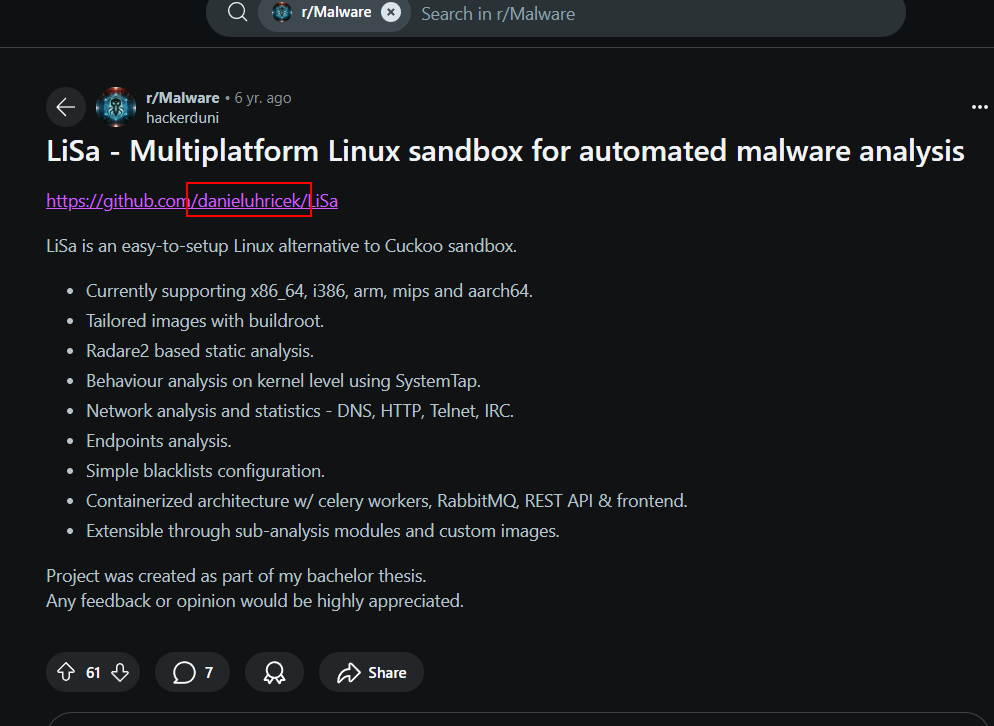
Then I found someone posted this tool on r/Malware reddit which have different username which was accepted as the answer of this Q.
Answer
danieluhricekQ2) Sample1: Analyse the sample using the sandbox. Is the binary stripped? What architecture is the sample based on and where is the entry point? (Format: Yes/No, Architecture, Entrypoint)
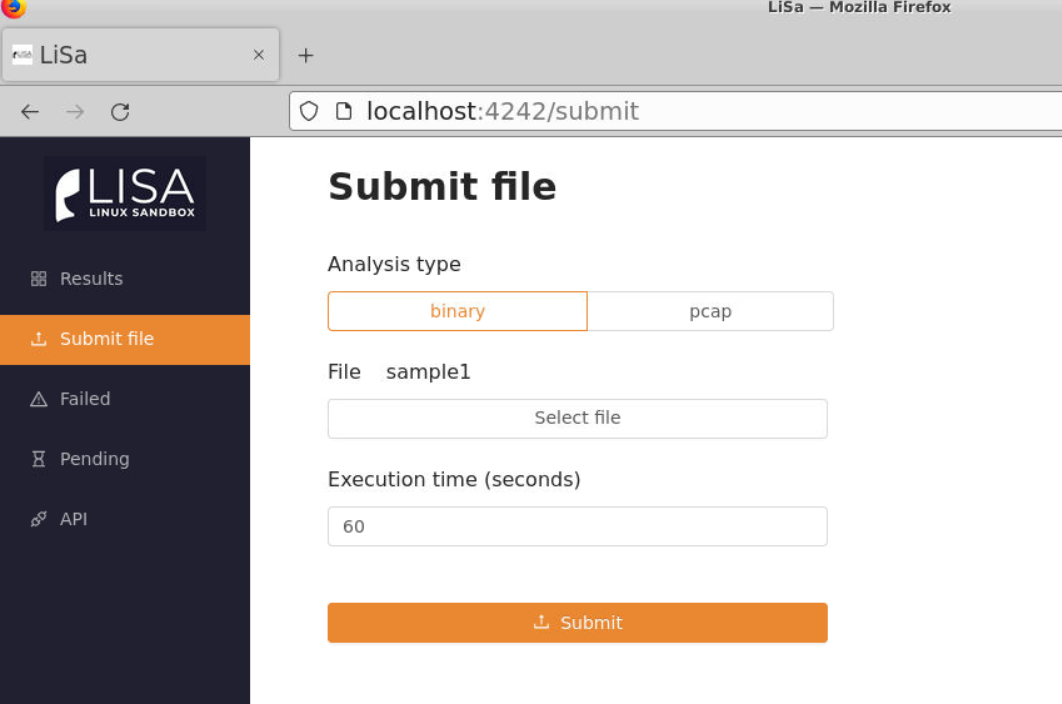
Lets navigate to lisa sandbox then go to "Submit file" > Select "binary" type > Select file then submit.
After submit, you will see this message appear and we will have to wait before our result will be shown on Results page
*I re-deployed my investigation machine
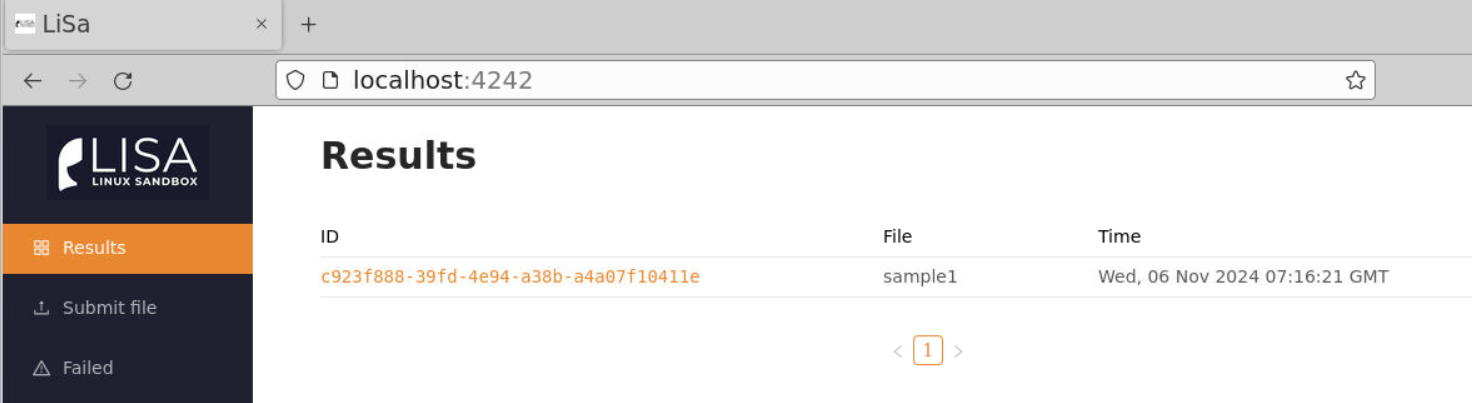
We can see that after a while, a result will be listed here and we can click task_id to view the result.
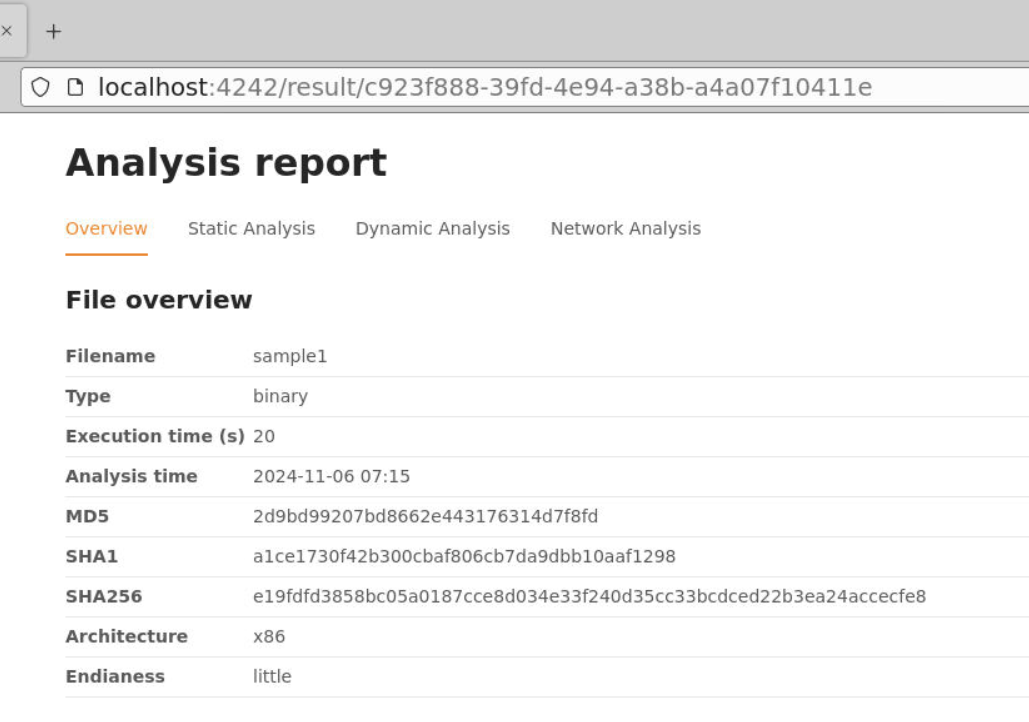
Lisa sandbox separate result into 4 report from Overview, Static Analysis, Dynamic Analysis and Network Analysis and we already architecture from this Overview report.
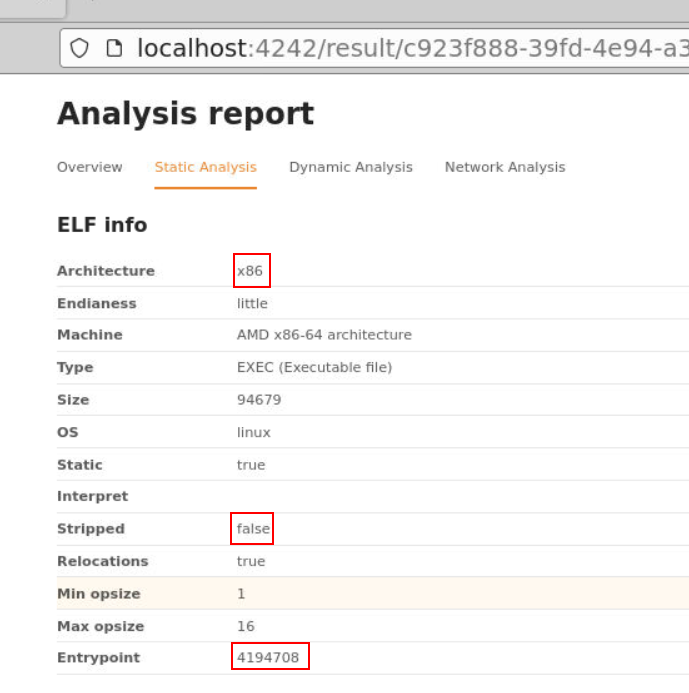
We can find the rest from Static Analysis report right here.
Answer
no, x86, 4194708Q3) Sample1: The malware attempts to reach out to a C2 domain. Name the IP and port that it attempts to reach out to. Also, where is this C2 located? (Format: X.X.X.X, Port, Country)
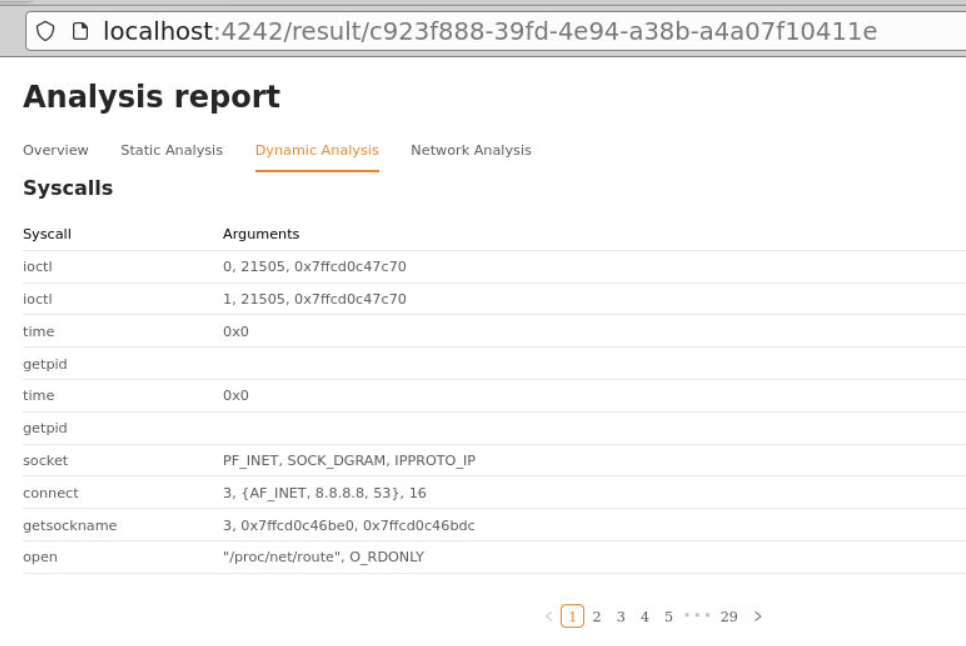
We will find IP address of C2 from Syscalls under Dynamic Analysis report but do not confuse with this google IP address that connect to port 53 for DNS
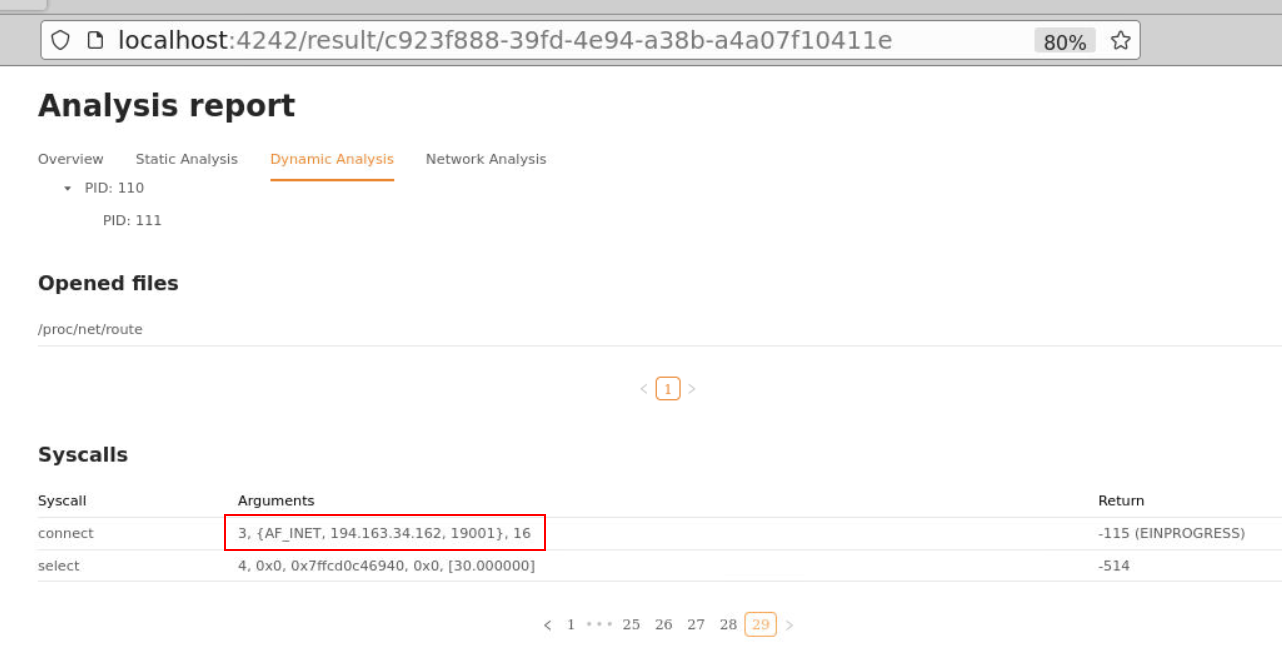
Instead the IP address along with port is in the last page of Syscalls record.
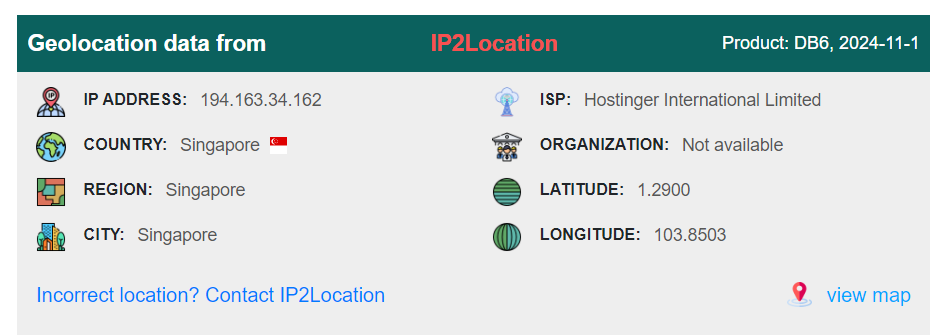
But upon searching for the country, we will get Singapore which is not the correct answer of this question but why?
Well.. something has been changed so the answer is Gernamy
Answer
194.163.34.162, 19001, GermanyQ4) \Sample1: Examine the domain in URLHaus. What is the name of the shell script that is used to execute the malware on the victim machine and who reported the shell script to URLHaus? (Format: Script.ext, reporter)
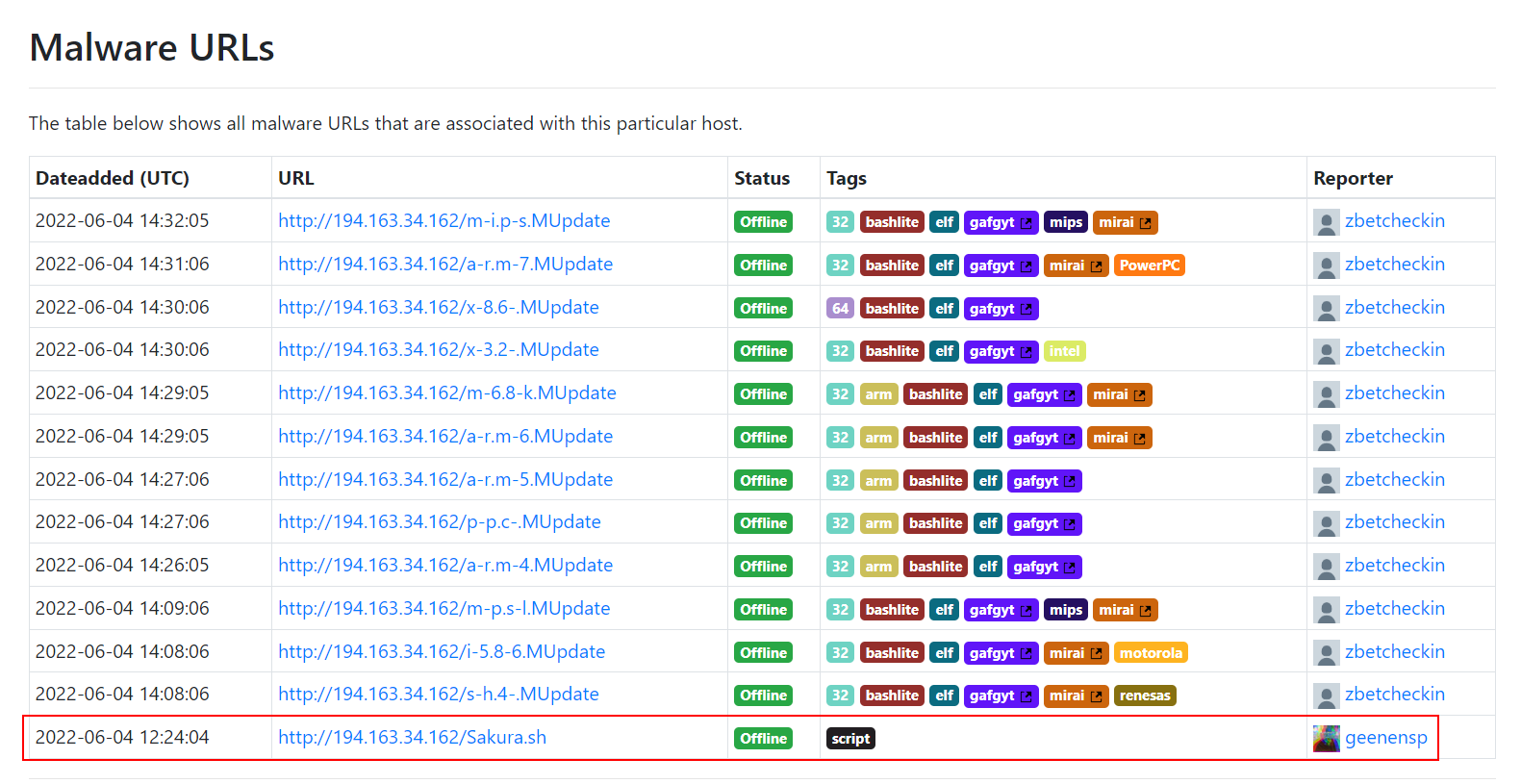
I started by searching MD5 of this file on URLHaus which lead to this Malware URLs and the answer of this question is the only bash script from these URLs.
Answer
Sakura.sh, geenenspQ5) Sample2: Analyse the PCAP with the sandbox. Two scans are noted in the anomalies section. Name them in alphabetical order (Format: Scan1, Scan2)
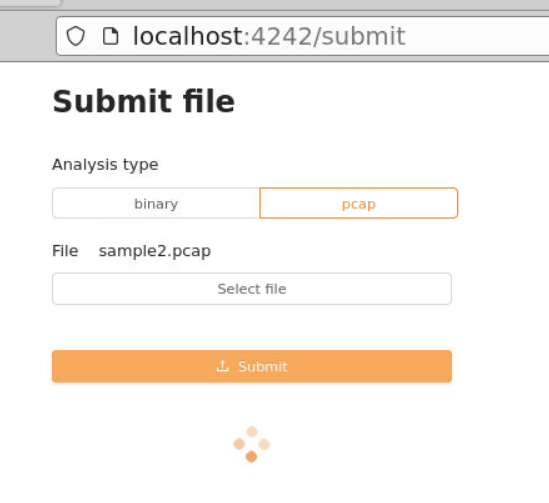
Lets go back to submit page and submit pcap file.
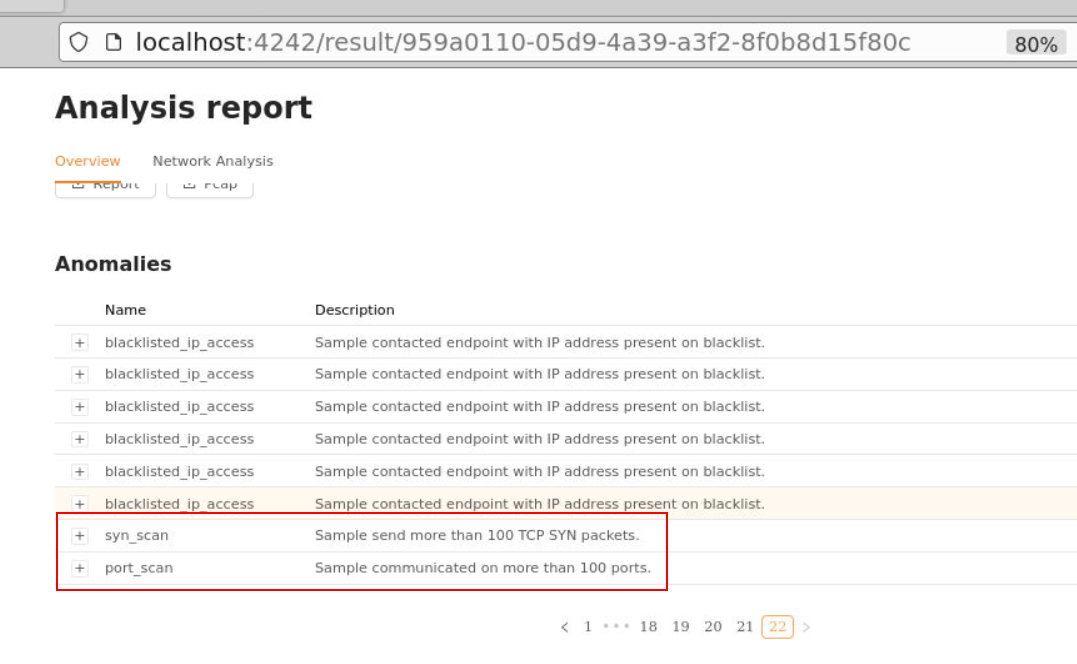
There are a lot of "blacklistedipaccess" anomalies but answers of this question come from the last page right here.
Answer
port_scan, syn_scanQ6) Sample2: A large exploit from 2021 is attempting to be exploited in the traffic with a base64 payload. What is the name of this vulnerability and the interface it’s exploiting? (Format: Vulnerability, Full name of the interface)
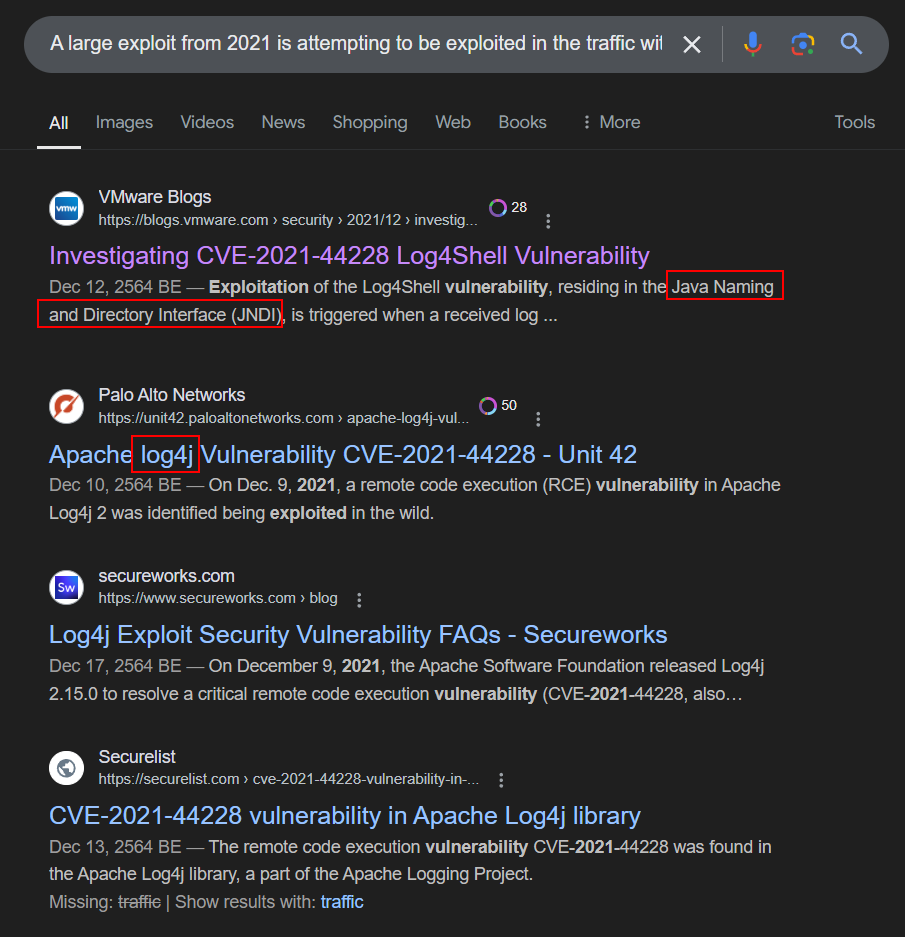
The most popular on the 2021 has to be Log4Shell vulnerability or we could see its vulnerability that exploit JNDI of log4j.
Answer
Log4j, Java Naming and Directory Interface https://blueteamlabs.online/achievement/share/52929/109
https://blueteamlabs.online/achievement/share/52929/109